Executive Summary
We identified an OS command injection vulnerability (CVE-2026-6644) in the PPTP VPN Client of ASUSTOR ADM that allows an authenticated administrator to execute arbitrary commands with root privileges, and reported it to ASUSTOR.
The vulnerability was reported as a zero-day with no public disclosure at the time of discovery, and has since been fixed in ADM 5.1.3.RGO1. ASUSTOR has rated it as Critical with a CVSS v4.0 Base Score of 9.4.
Censys revealed a significant number of internet-facing hosts potentially associated with ASUSTOR. We estimate up to approximately 19K hosts as an upper-bound exposure estimate of ASUSTOR-related assets. This figure does not imply that all hosts are running an affected version, using a vulnerable configuration, or susceptible to this specific vulnerability.
ASUSTOR ADM users are advised to update to ADM 5.1.3.RGO1 or later, restrict management interface access from the WAN, and set a strong administrator password.
Overview
We discovered and responsibly disclosed a now-fixed zero-day vulnerability in the PPTP VPN Client feature of ASUSTOR ADM.
The vulnerability, tracked as CVE-2026-6644, is an authenticated OS command injection issue in /portal/apis/settings/vpn.cgi. The PPTP server address parameter is written into a pppd configuration file’s pty directive without proper escaping or sanitization. Since pppd executes the pty value through /bin/sh, this allows an authenticated administrator to break out of the restricted web environment and execute arbitrary commands on the underlying operating system.
ASUSTOR rated the individual CVE as Critical with a CVSS v4.0 Base Score of 9.4.
Detailed Vulnerability
The PPTP VPN connection handler in /portal/apis/settings/vpn.cgi writes the
server address parameter into a pppd configuration file’s pty directive
without any escaping or sanitization. pppd executes the pty value via
/bin/sh, resulting in root-level command execution.
The same function does apply single-quote escaping to the username (acc)
and password (pass) parameters, but omits this escaping for the server
address — indicating an implementation oversight.
Administrator authentication is required.
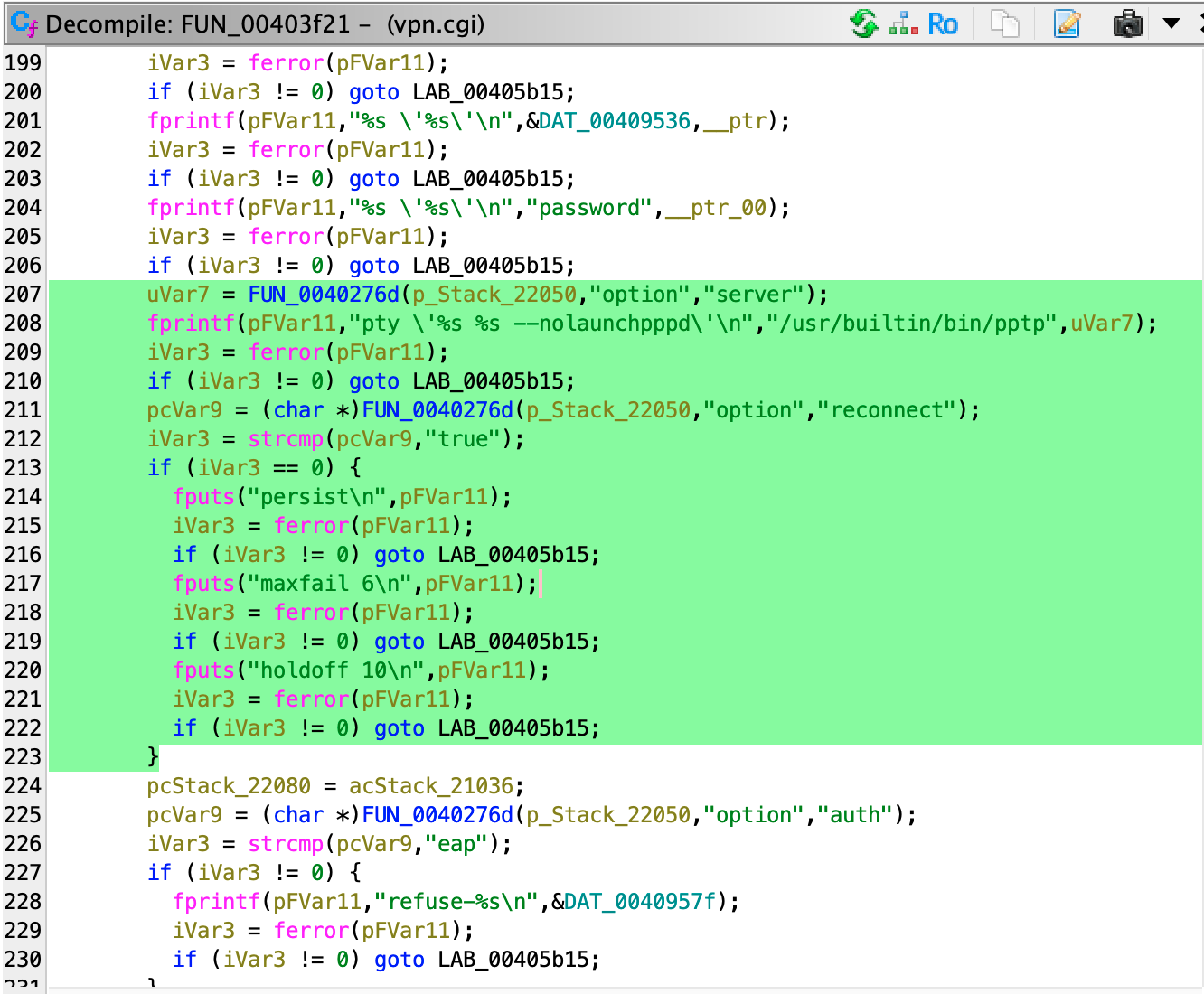
The connect handler function FUN_00403f21 in vpn.cgi retrieves the PPTP
server address (line 207) and passes it directly to fprintf (line 208)
with no escaping applied between the two calls:
PoC and Verification Results
The provided script is a minimal local reproducer. It does not connect to or exploit any ASUSTOR device.
The script reproduces the vulnerable fprintf format and the pppd /bin/sh -c
execution in Python: poc_CVE-2026-6644_pptp_injection.py
Threat Scenario and Impact
Exploitation of this vulnerability requires administrator authentication to the ADM management interface. It is therefore not a pre-authentication RCE.
However, ADM’s default administrator account uses admin for both username and password. Environments where default credentials remain unchanged are at elevated risk. Once an attacker gains administrator access to ADM, this vulnerability enables arbitrary command execution on the NAS with root privileges.
A compromised NAS could be leveraged for malware installation, persistence, data access, DDoS infrastructure, or residential proxy abuse.
Exposure Estimate
We used Censys to estimate an upper bound on internet-facing ASUSTOR-related hosts.
This estimate does not represent the number of confirmed vulnerable hosts. The results may include hosts that have already applied the patch, hosts running unaffected versions, hosts not using the PPTP VPN feature, or hosts that simply match an ASUSTOR-related fingerprint.
We therefore treat this figure not as the number of vulnerable hosts, but as an upper-bound exposure estimate of ASUSTOR-related internet-facing assets. At the host level, up to approximately 19K hosts may be ASUSTOR-related.
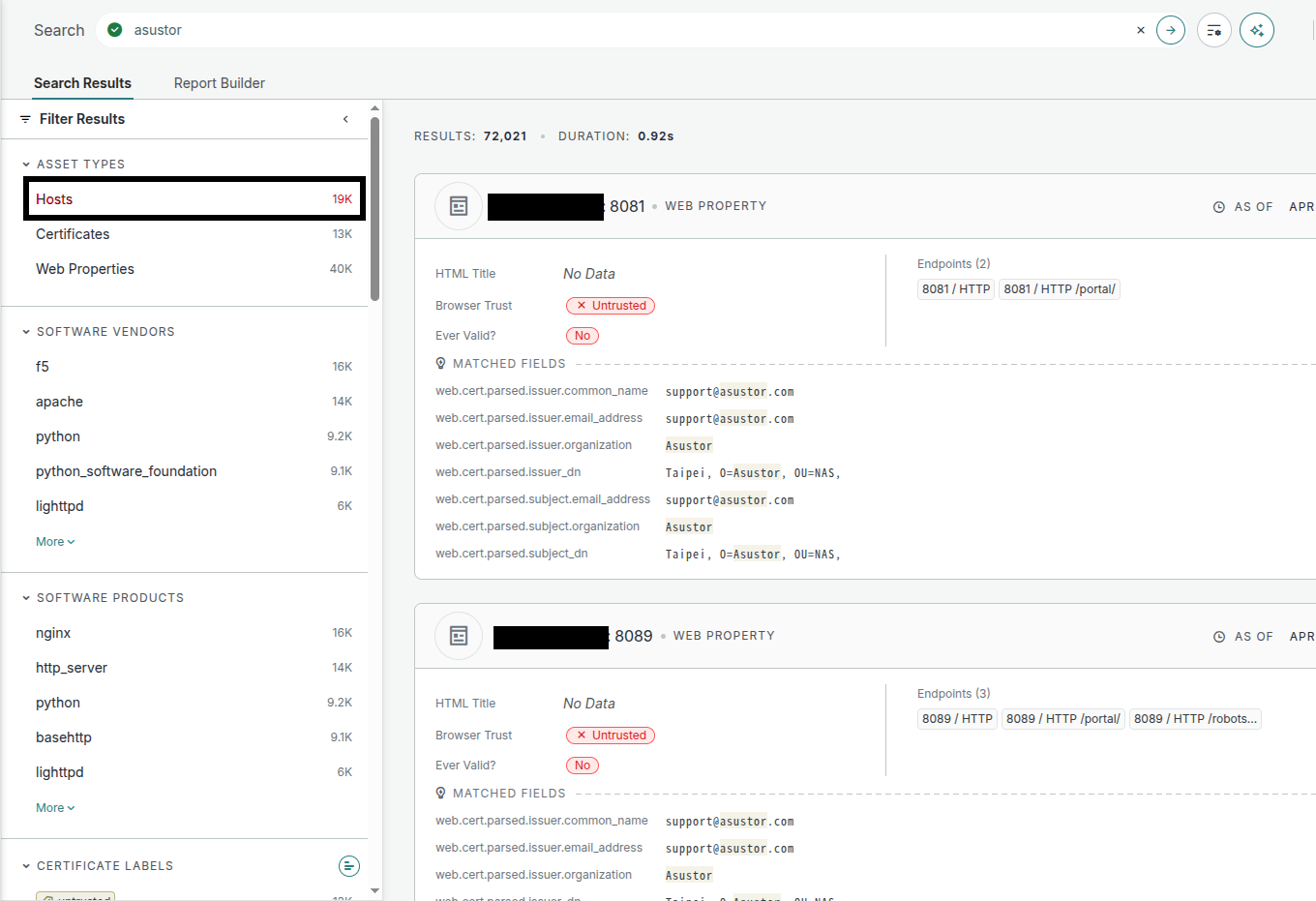
Figure: Censys-based upper-bound estimate of internet-facing ASUSTOR-related hosts. This is not the number of confirmed vulnerable devices.
Mitigation
According to ASUSTOR’s advisory, the vulnerability has been fixed in ADM 5.1.3.RGO1. ADM users are advised to update to the latest available firmware.
As this vulnerability requires administrator authentication, the following mitigations are also important:
- Do not expose the ADM management interface directly to the WAN
- Restrict management interface access to trusted networks
- Do not use the default or a weak administrator password
- Disable unnecessary services
- Administer the device over a VPN where possible
NAS management interfaces should not be directly exposed to the internet unless absolutely necessary.
Conclusion
CVE-2026-6644 is a now-fixed authenticated root command injection vulnerability in the PPTP VPN Client of ASUSTOR ADM.
While not a pre-authentication RCE, ASUSTOR rated this individual CVE as Critical with a CVSS v4.0 Base Score of 9.4. Successful exploitation allows an attacker to break out of the restricted web environment and execute arbitrary commands on the underlying OS, leading to full system compromise.
Our Censys-based search confirmed a notable number of internet-facing hosts associated with ASUSTOR. We estimate an upper bound of approximately 19K hosts. This is not the number of confirmed vulnerable devices, and does not imply that all hosts are running the affected version, configuration, or are susceptible to this vulnerability.
ASUSTOR ADM users are advised to update to the patched firmware, restrict management interface access from the WAN, and set a strong administrator password.